Introduction
During the same security research on ProjeQtOr, we identified another interesting vulnerability, this time in the plugin upload mechanism.
I already introduced what ProjeQtOr is and why it can contain sensitive business data in the first article of this series: From login to admin : CVE-2026-41462 .
This vulnerability is different from the SQL injection one. Instead of attacking the database directly, it abuses the way the application extracts uploaded plugin archives.
For this vulnerability, the application extracts ZIP files on the server without proper validation of the file paths, which can allow an attacker to write files outside of the intended plugin directory, this can lead to remote code execution. Chaining this with the previous SQL injection vulnerability, an attacker can go from no access to full server compromise.
Vulnerability summary
The vulnerability is a ZipSlip path traversal in the plugin upload feature.
In short, when the application receives a ZIP archive, it extracts its content on the server. The issue is that the paths inside the archive were not properly checked before extraction.
The vulnerable logic was based on an unsafe archive extraction pattern:
1$za->extractTo($uploaddir);
This kind of code looks harmless at first, but it can become dangerous if the archive contains file paths that resolve outside of the intended destination directory.
Instead of extracting only plugin files inside the plugin folder, a malicious archive could force the application to write files elsewhere on the filesystem.
Attack surface
The vulnerable code path was reachable through the plugin upload feature.
Once we have access to the the plugin upload feature, we can upload a crafted ZIP file containing a path traversal such as ../../shell.php, this file will be extracted outside the intended plugin directory and can be accessed through the web server, allowing us to execute arbitrary code on the server.
This makes the vulnerability especially dangerous in environments where plugin upload is exposed to privileged or semi-privileged users.
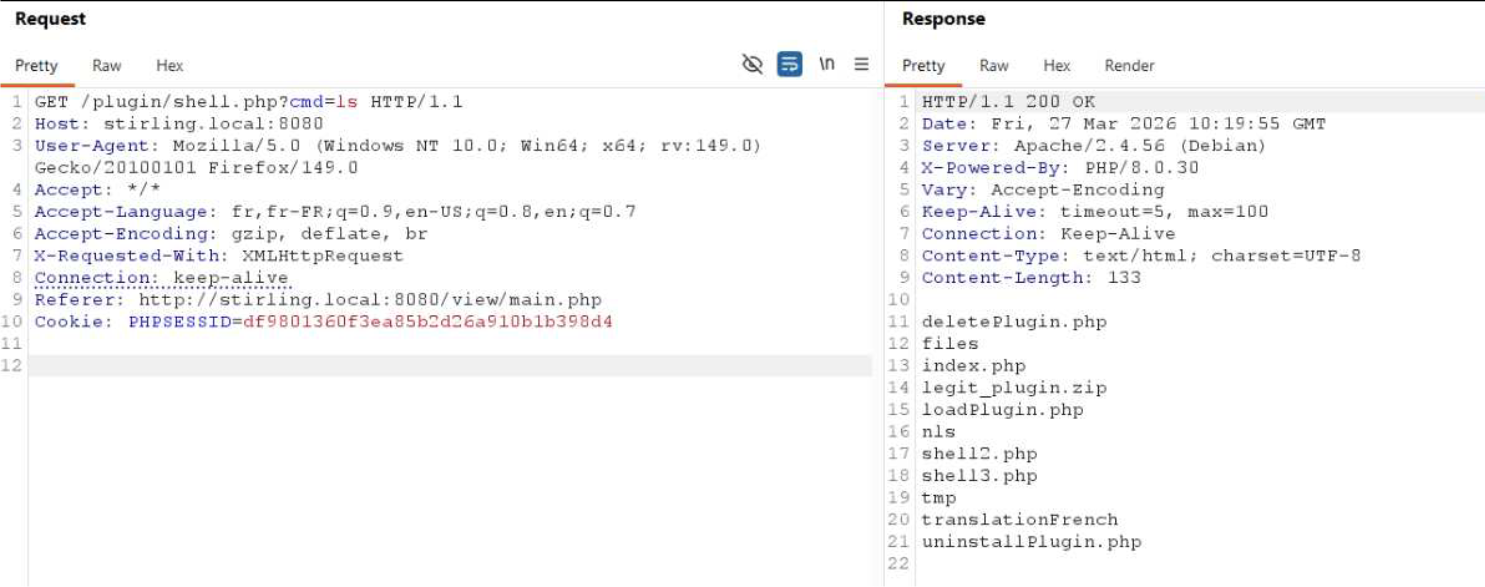
Proof of concept
No exploit payload is provided in this article.
But here is the result of the exploited vulnerability:
Recommended fix
The extraction logic should validate every file path before writing anything to disk.
A safe implementation should:
- extract archives file by file instead of blindly calling
extractTo(); - normalize each destination path;
- reject absolute paths;
- reject paths containing traversal sequences;
- ensure that the final resolved path stays inside the expected directory;
- refuse active server-side extensions where they are not needed;
- store uploaded content outside of the web root when possible.
It is also a good idea to treat plugin installation as a highly privileged action, because plugins usually have a direct impact on the application runtime.
Conclusion
Always be cautious with file uploads, not just with the file types and extensions, but also with the content of the archives.
This was a good RCE vulnerability to find, and with the previous SQL injection vulnerability, that is 2 critical vulnerabilities found, but there are still others, thanks for reading this article !
Disclaimer
This post is for educational purposes only. Do not attempt to exploit this vulnerability on systems you do not own or have explicit permission to test on. Always follow responsible disclosure practices when reporting security issues.